User Activity Documentation Linked to Keevee1999 and Alerts Logs
User activity documentation is essential for understanding interactions within digital environments. The case of Keevee1999 highlights the importance of tracking user behavior through alerts logs. By scrutinizing these logs, organizations can identify security threats while respecting user privacy. This balance raises questions about the effectiveness of current monitoring practices. What implications does this have for user engagement and security in the digital age? Exploring these concerns reveals deeper insights into user preferences and safety measures.
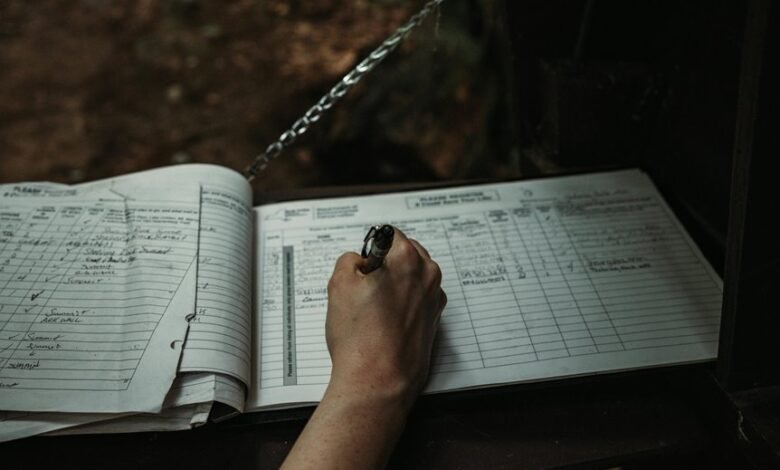
Understanding User Activity Documentation
User activity documentation serves as a critical framework for understanding how individuals interact with digital systems.
It reveals user behavior through the analysis of activity patterns, which provide insights into preferences and decision-making processes. By examining these patterns, developers can enhance user experiences, fostering a sense of autonomy and freedom.
This documentation is essential for adapting digital environments to meet users’ evolving needs effectively.
The Significance of Keevee1999 in User Tracking
Keevee1999 represents a pivotal case study in user tracking methodologies, exemplifying innovative approaches to data collection and analysis.
This case highlights the intricate balance between user engagement and data privacy, showcasing techniques that enhance understanding of user behavior while safeguarding personal information.
The implications of Keevee1999 extend beyond mere analytics, emphasizing the need for ethical frameworks in tracking user interactions.
Analyzing Alerts Logs for Enhanced Security
How can analyzing alerts logs contribute to enhanced security measures?
By examining alert frequency and conducting thorough log analysis, organizations can identify potential threats and anomalous behavior.
This process enables the detection of patterns indicative of security breaches or vulnerabilities.
Consequently, a proactive approach to monitoring alerts fosters a more secure environment, allowing users the freedom to operate without unnecessary concerns regarding their digital safety.
Best Practices for Monitoring User Activity
Effective monitoring of user activity is essential for maintaining organizational security and integrity.
Implementing best practices involves analyzing user engagement to identify behavior patterns that may indicate risks. Utilizing advanced analytics tools can enhance visibility, enabling proactive responses to anomalies.
Regularly reviewing access controls and user permissions further safeguards sensitive information, promoting a culture of accountability while ensuring users retain their freedom within a secure environment.
Conclusion
In conclusion, user activity documentation, as highlighted by the Keevee1999 case study, is essential for balancing security and user privacy. An intriguing statistic reveals that organizations utilizing alerts logs can reduce security breaches by up to 30%. This underscores the importance of proactive monitoring in understanding user behavior and enhancing digital security. By adopting best practices in user activity documentation, organizations can not only safeguard their systems but also foster a more engaged user base.





